I love that the local translation feature is getting regular small updates to make it more useable. It's a great feature.
Porges believes
This is an interesting article and yet you've chosen to quote the most speculative unscientific part of it from the final paragraph.
"Have you tried going outside" is not a scientific cure for depression.
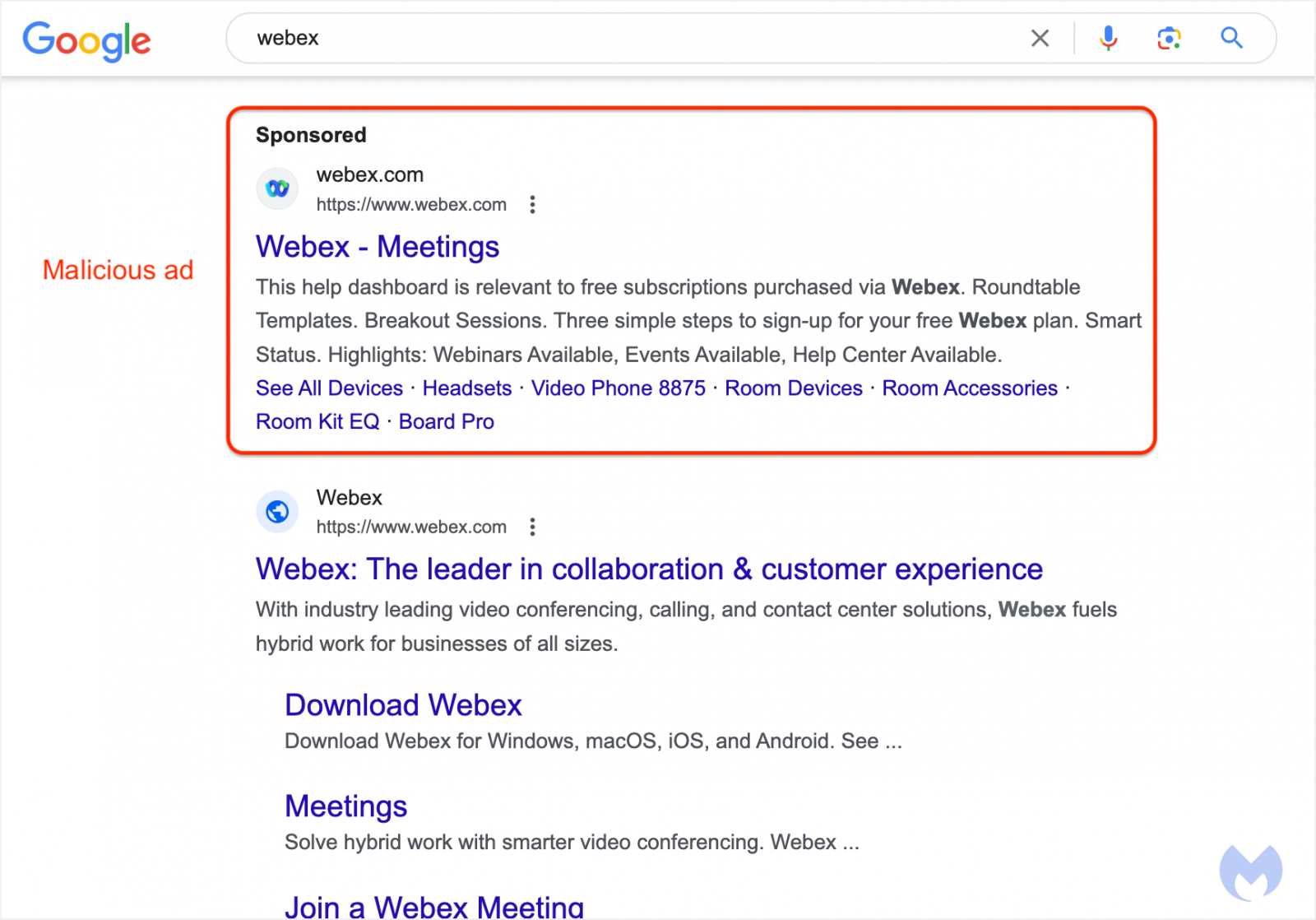
Note to readers: Don't install python dependencies for random python projects of unknown provenance. PyPI is regularly being used as a vector for distributing malware. See recent news stories here: https://www.bleepingcomputer.com/tag/pypi/
You should manually check every package listed in requirements.txt and verify that it is a trustworthy python library.
AI is definitely capable of making great music right now.
Got any links?
It was more than just a special icon for a folder, it had special behaviour too. Without looking it up (in the spirit of the meme), I seem to remember that it would automatically sync the files any time that you insert the floppy disk, kind of like having Dropbox but without the internet. The idea being that you would have files on your computer that you could take with you somewhere else (in your briefcase, on a floppy disk) and all instances of that briefcase would automatically sync the latest updates of the files without you having to manually copy them and work out which was the latest version of a file.
a really odd way of using Git
Git was literally designed for kernel development.
The translation feature is based on the Bergamot project to provide users with a privacy-aware translation engine where the translation is done locally using machine learning, it’s never sent to a third party, and it’s optimized for consumer hardware.
Neat!
Saved you a click:
A common allele of HLA is associated with asymptomatic SARS-CoV-2 infection
We observed that individuals carrying this common allele (approximately 10% in individuals with European ancestry) are more than twice as likely to remain asymptomatic after SARS-CoV-2 infection compared with those who do not, and a notable effect of HLA-B*15:01 homozygosity increasing the chance of remaining asymptomatic by more than eight times.
Together, our results strongly support the hypothesis that HLA-B*15:01 mediates asymptomatic COVID-19 disease through pre-existing T cell immunity due to previous exposure to HKU1-CoV and OC43-CoV.
XMPP did not exist on its own outside of nerd circles, while ActivityPub enjoys the support and brand recognition of Mastodon.
Jabber was widely used in the early 2000s and not just among "nerds." But Rochko would have only been 7+ years old at the time so how would he know that.
The "brand recognition of Mastodon" part makes me think this has to be a joke... right?
If it was plausible this would be bigger news. There's a claim like this every couple of months and none have held up to scrutiny so far.