view the rest of the comments
Bikini Bottom Twitter
Ahoy, me buckos! Welcome to Bikini Bottom Twitter! Your digital reef for the latest salty gossip and treasure tales! And while you're at it, be sure to drop by the Krusty Krab for a delicious Krabby Patty so I can get yer mon- err I mean, 'cause they're the best treat under the sea!
Rule 1 - This is Bikini Bottom Twitter, all posts should be Spongebob related in "(Old-School) Twitter-like" form
Rule 2 - Political posts, as long as it follows rule 1, will be permitted, so long as you behave yourselves.
Bikini Bottom Municipal Code §33-07: Anti-Tankie Ordinance Residents are prohibited from circulating tankie ideology or other authoritarian propaganda on Bikini Bottom Twitter. Offenders will be permanently banned from BPT by the BBPD faster than Plankton is ejected from The Krusty Krab.
Rule 3 - Please no reposts within the last couple days, at least
Rule 4 - All posts should be at least above a "Squirdward-krusty-krab-shift" level of effort
Rule 5 - Be chill, be a Patrick not a squidward.
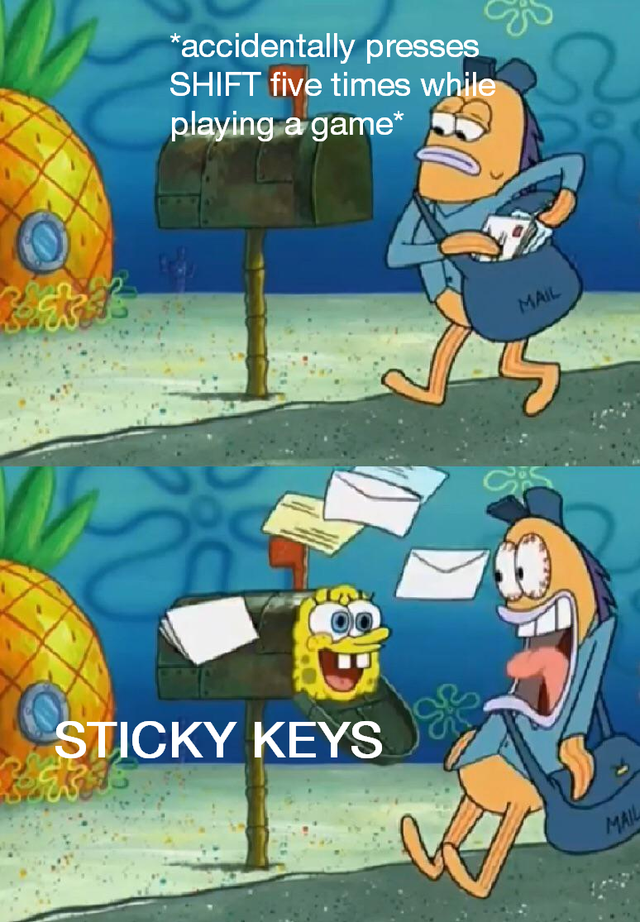
It's a well known exploit on Windows:
Now, you can change all the passwords on the system from the login screen.
Last I checked, it still works, and it's been around since xp days.
Don't you need to be admin to muck with system32?
Just access to the hard drive. A bootable Linux USB could do that. I think you can get there through some obscure way with windows installation media as well.