Anytime you see a password length cap you know they are not following current security standards. If they aren't following them for something so simple and visible, you'd better believe it's a rat infested pile of hot garbage under the hood, as evidenced here.
you have to limit it somewhere or you're opening yourself up for a DoS attack
password hashing algorithms are literally designed to be resource intensive
Edited to remove untrue information. Thanks for the corrections everyone.
Incorrect.
They're designed to be resource intensive to calculate to make them harder to brute force, and impossible to reverse.
Some literally have a parameter which acts as a sliding scale for how difficult they are to calculate, so that you can increase security as hardware power advances.
Hashes are one way functions. You can’t get from hash back to input
Only if the hash function is designed well
See "Password Hashing" here: https://en.m.wikipedia.org/wiki/Key_derivation_function
It is actually important to have a controlled cost to calculate in the forward direction too.
Are you saying that any site which does not allow a 27 yobibyte long password is not following current security standards?
I think a 128 character cap is a very reasonable compromise between security and sanity.
Atleast this is reasonable, I have seen some website don't allow more than 6 character.
WTF? Are they trying to get hit with brute force attacks?
At least it's 128
I had a phone carrier that changed from a pin to a "password" but it couldn't be more than 4 characters
At my job they just forced me to use a minimum 15-character password. Apparently my password got compromised, or at least that was someone’s speculation because apparently not everyone is required to have a 15-char password.
My job is retail, and I type my password about 50 times a day in the open, while customers and coworkers and security cameras are watching me.
I honestly don’t know how I’m expected to keep my password secure in these circumstances. We should have physical keys or biometrics for this. Passwords are only useful when you enter them in private.
Yeah you should have a key card. Like not even from a security perspective but from an efficiency one. Tap a keycard somewhere that would be easily seen if an unauthorized person were to even touch or even swipe it if need be. I’m sick and tired of passwords at workplaces when they can be helped
In theory yes. But in practice the DB will almost always have some cap on the field length. They could just be exposing that all the way forward. Especially depending on their infastructure it could very well be that whatever modeling system they use is tightly integrated with their form generation too. So the dev (junior or otherwise) thought it would be a good idea to be explicit about the requirement
That said, you are right that this is still wrong. They should use something with a large enough cap that it doesn't matter and also remove the copy telling the use what that cap is
Hashing will make every password the same length.
Right but that puts a limit on the hash algorithm’s input length. After a certain length you can’t guarantee a lack of collisions.
Of course the probability stays low, but at a certain point it becomes possible.
Collisions have always been a low concern. If, for arguments sake, I.hate.password. had a collision with another random password like kag63!gskfh-$93+"ja the odds of the collision password being cracked would be virtually non-existent. It's not a statistically probable occurrence to be worried about.
yup yup. Forgot we were talking about a protected field and not just raw data
You misunderstand the issue. The length of the password should not have any effect on the size of the database field. The fact that it apparently does is a huge red flag. You hash the password and store the hash in the db. For example, a sha256 hash is always 32 bytes long, no matter how much data you feed into it (btw, don’t use sha256 to hash passwords, it was just an example. It’s not a suitable password hashing algorithm as it’s not slow enough).
ur absolutely right. Idk why I was thinking about it like a normal text/char field
[This comment has been deleted by an automated system]
I know this a a joke, but please use a password manager, it is such a game changer.
Bitwarden is free and E2E encrypted and if you want additonal feature, they only cost 10 bucks pre year. You can even use it with anonaddy to hide your email, which is also totally free and open source.
What are those premium features? I never felt like I was missing something from the free bitwarden
You can have it generate 2FA TOTP.
2FA one time code was the reason I got premium (and obviously support FOSS project). It is a slight security downgrade, but a whole lot of QOL upgrade.
I also imagine hardware key support like yubikey would be very appealing for many.
yubikey/fido2 support is what I'd probably consider premium for
I’m already using Bitwarden but I hadn’t heard about anonaddy, thanks for the tip!
They work like a miracle together https://bitwarden.com/blog/add-privacy-and-security-using-email-aliases-with-bitwarden/
What is even more surprising is that even the free tier is perfectly usable, but consider paying if you have the money to support them.
I know it's annoying that the password "doesn't match", but ... a 128 character limit?! I'd like to see THAT fully utilized lol.
(PS: the sentence above is exactly 128 characters, just for a comparison.)
...and I bet once you want to change it you get the "your new password can not be the old password" error message just because.
An acquaintance of mine has a 36 characters long passcode for his tablet that he manually puts in every time he wants to use it.
And you can use password managers to make secure passwords without ever having to input them yourself.
That is a very good idea if you want to disincentivise yourself from using your tablet
He doesnt use it outside of school stuff and even then prefers to write things on paper, I dont think that he has to make disincentives.
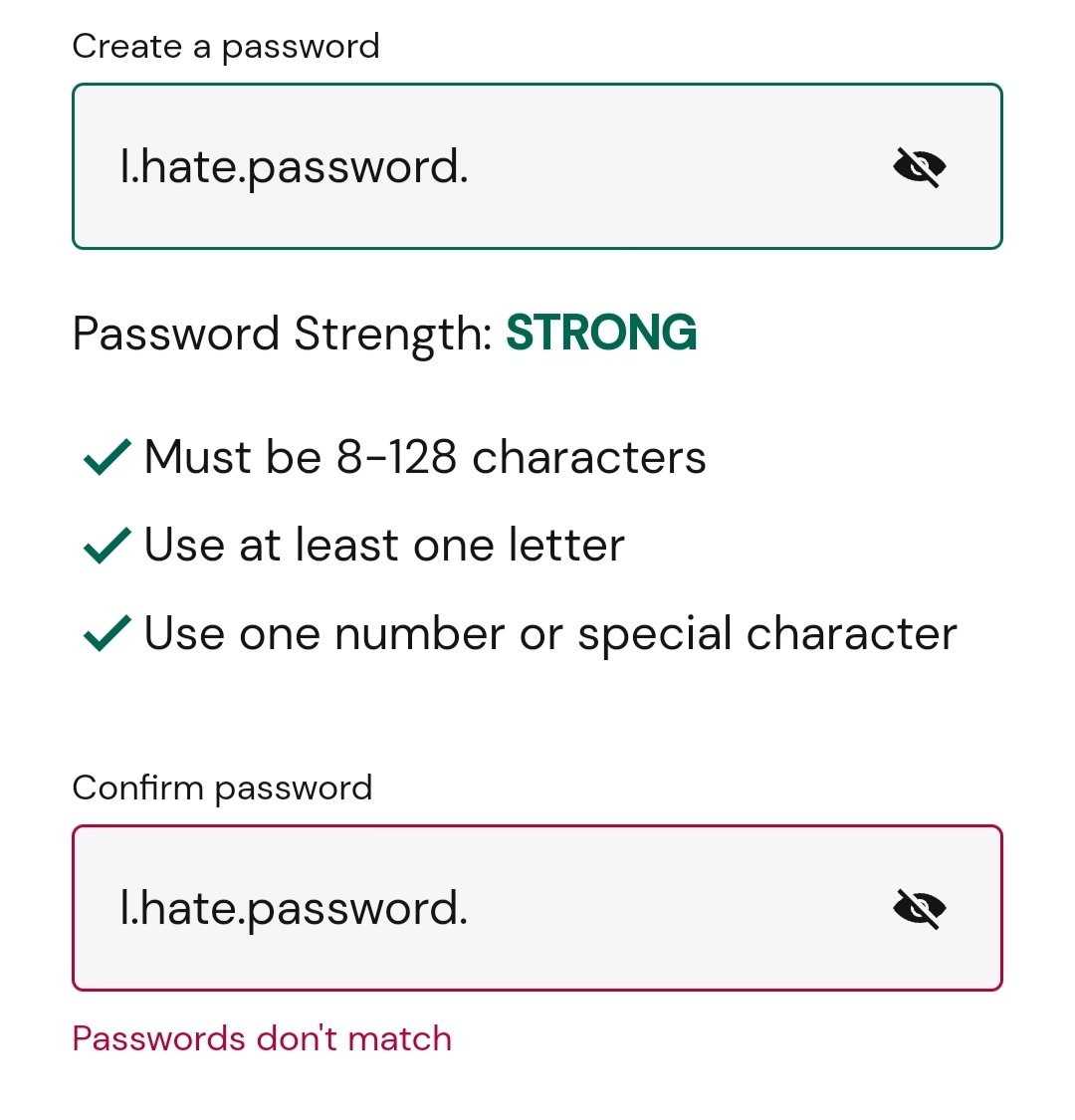
Those are L.hate… and i.hate…, am I seeing that correctly?
This is even more infuriating than getting "password incorrect" going in and getting a recovery password, then trying to change passwords to the one you initially used and getting "new password can't be the same as old password."
Yikes.... This thread is a wasteland of misinformation and mininformers arguing with other mininformers about who's misinformation is less ill informed.
This thread is:
- 50% technology illiteracy
- 25% Dunning Kruger valley
- 10% Actual knowledge
- Everyone else just here for the ride
This comment could just be copy-pasted to so many threads
Is there a software gore community yet?
Hi there! Looks like you linked to a Lemmy community using a URL instead of its name, which doesn't work well for people on different instances. Try fixing it like this: !softwaregore@lemmy.world
Did one get an autocorrect space after the .?
Mildly Infuriating
Home to all things "Mildly Infuriating" Not infuriating, not enraging. Mildly Infuriating. All posts should reflect that. Please post actually infuriating posts to !actually_infuriating@lemmy.world
I want my day mildly ruined, not completely ruined. Please remember to refrain from reposting old content. If you post a post from reddit it is good practice to include a link and credit the OP. I'm not about stealing content!
It's just good to get something in this website for casual viewing whilst refreshing original content is added overtime.
Rules:
1. Be Respectful
Refrain from using harmful language pertaining to a protected characteristic: e.g. race, gender, sexuality, disability or religion.
Refrain from being argumentative when responding or commenting to posts/replies. Personal attacks are not welcome here.
...
2. No Illegal Content
Content that violates the law. Any post/comment found to be in breach of common law will be removed and given to the authorities if required.
That means: -No promoting violence/threats against any individuals
-No CSA content or Revenge Porn
-No sharing private/personal information (Doxxing)
...
3. No Spam
Posting the same post, no matter the intent is against the rules.
-If you have posted content, please refrain from re-posting said content within this community.
-Do not spam posts with intent to harass, annoy, bully, advertise, scam or harm this community.
-No posting Scams/Advertisements/Phishing Links/IP Grabbers
-No Bots, Bots will be banned from the community.
...
4. No Porn/Explicit
Content
-Do not post explicit content. Lemmy.World is not the instance for NSFW content.
-Do not post Gore or Shock Content.
...
5. No Enciting Harassment,
Brigading, Doxxing or Witch Hunts
-Do not Brigade other Communities
-No calls to action against other communities/users within Lemmy or outside of Lemmy.
-No Witch Hunts against users/communities.
-No content that harasses members within or outside of the community.
...
6. NSFW should be behind NSFW tags.
-Content that is NSFW should be behind NSFW tags.
-Content that might be distressing should be kept behind NSFW tags.
...
7. Content should match the theme of this community.
-Content should be Mildly infuriating. If your post better fits !Actually_Infuriating put it there.
-The Community !actuallyinfuriating has been born so that's where you should post the big stuff.
...
8. Reposting of Reddit content is permitted, try to credit the OC.
-Please consider crediting the OC when reposting content. A name of the user or a link to the original post is sufficient.
...
...
Also check out:
Partnered Communities:
Reach out to LillianVS for inclusion on the sidebar.
All communities included on the sidebar are to be made in compliance with the instance rules.