view the rest of the comments
Selfhosted
A place to share alternatives to popular online services that can be self-hosted without giving up privacy or locking you into a service you don't control.
Rules:
-
Be civil: we're here to support and learn from one another. Insults won't be tolerated. Flame wars are frowned upon.
-
No spam posting.
-
Posts have to be centered around self-hosting. There are other communities for discussing hardware or home computing. If it's not obvious why your post topic revolves around selfhosting, please include details to make it clear.
-
Don't duplicate the full text of your blog or github here. Just post the link for folks to click.
-
Submission headline should match the article title (don’t cherry-pick information from the title to fit your agenda).
-
No trolling.
-
No low-effort posts. This is subjective and will largely be determined by the community member reports.
Resources:
- selfh.st Newsletter and index of selfhosted software and apps
- awesome-selfhosted software
- awesome-sysadmin resources
- Self-Hosted Podcast from Jupiter Broadcasting
Any issues on the community? Report it using the report flag.
Questions? DM the mods!
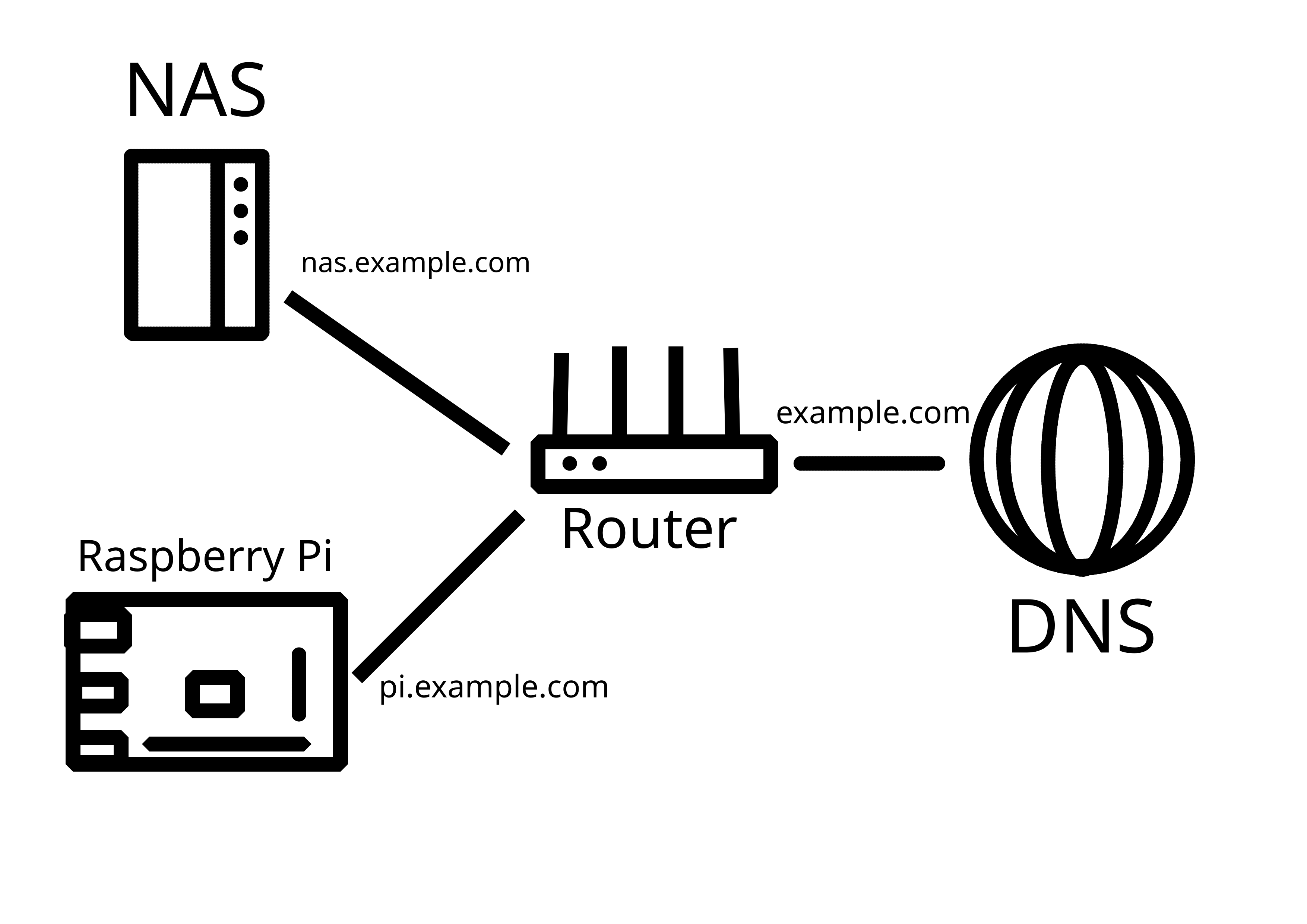
Who is externally reaching these servers?
Joe public? Or just you and people you trust?
If it's Joe public, I wouldn't have the entry point on my home network (I might VPS tunnel, or just VPS host it).
If it's just me and people I trust, I would use VPN for access, as opposed to exposing all these services publicly
Your stuff is more likely to get scanned sitting in a VPS with no firewall than behind a firewall on a home network
Just me and the people I trust, but there are certain inconveniences around using VPN for access.
First, I live in the jurisdiction that is heavily restrictive, so VPN is commonly in use to bypass censorship
Second, I sometimes access my data from computers I trust but can't install VPN clients on
Third, I share my NAS resources with my family, and getting my mom to use a VPN every time she syncs her photos is near impossible
So, fully recognizing the risks, I feel like I have to expose a lot of my services.
Remember that with services facing public internet it's not about if you get hacked but when you get hacked. It's personal photos on someone elses hands then.
Not sure why you're downvote, you're absolutely right. People scan for open ports all day long and will eventually find your shit and try to break in. In my work environment, I see thousands of login attempts daily on brand new accounts, just because something discovered they exist and want to check it out.
I do remember that and take quite a few precautions. Also, nothing that can be serioisly used against me is in there.