I know, right... Damn foss enthusiasts, you show 'em sources in order to get some cheap publicity, and those bastards immediately start raising a stink over you slightly attempting to fuck them over with licensing
The sources are released under a source-available license, you are legally prohibited from reading them
All clothes are no-iron clothes if you DGAF enough :)
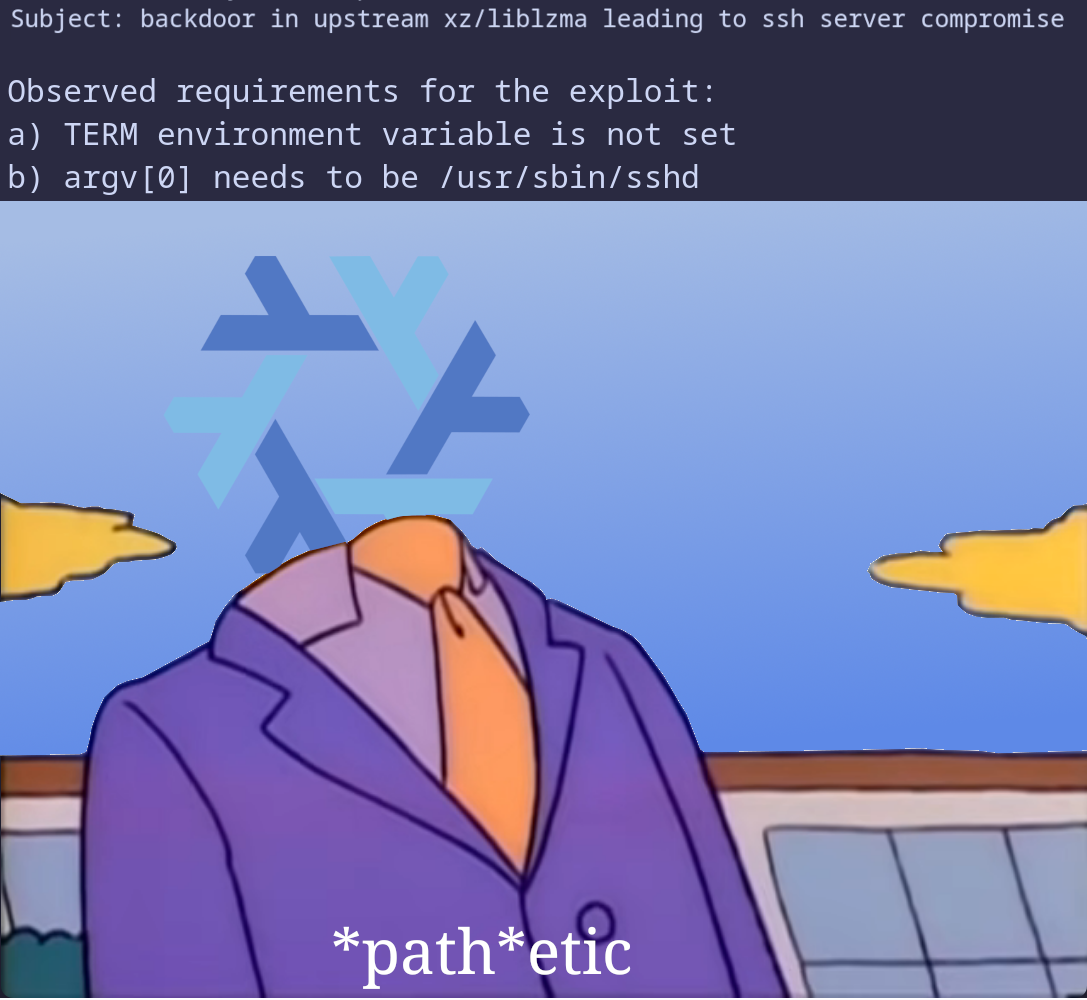
Incorrect: the backdoored version was originally discovered by a Debian sid user on their system, and it presumably worked. On arch it's questionable since they don't link sshd with liblzma (although some say some kind of a cross-contamination may be possible via a patch used to support some systemd thingy, and systemd uses liblzma). Also, probably the rolling opensuse, and mb Ubuntu. Also nixos-unstalbe, but it doesn't pass the argv[0] requirements and also doesn't link liblzma. Also, fedora.
| what if you | wanted to show a presentation |
|---|---|
| but windows said |  |
This is good, but I prefer this 
Should've installed linux 🤷
Nixos is at 23.11 :) Also, rolling releases are kinda fun: the latest commit so far is 46ae0210ce163b3cba6c7da08840c1d63de9c701 which roughly translates to nixos-unstable 403509863565239228514588166489915404446713104129 :D
Yeah, those mailing lists used to have some quite funny stuff; my favorite so far is smth along the lines of "whoever thought this was a good idea should be retroactively aborted".
But, on the other hand, damn it's toxic. Should've really sucked to work on the kernel back then.
Replace kali with nixos, and it'd be accurate 😁 Also, gentoo.
And Kali is more like "are you older than 13 → no"





* the sound of buffalos approaching *